Preventing Play Store Apps from Updating Automatically
With the increased adoption of managed Android devices, a common request is to prevent Play Store apps from updating. For example, you might not want to receive Chrome updates because you have validated your hybrid app against a specific version of the web engine. This guide will talk through how to achieve that.
Until recently there was no good solution to this problem and administrators were faced with an all-or-nothing approach, either prevent or allow ALL updates from the Play Store.
Mobility eXtensions (MX) version 10.3 solves the problem of only wanting specific Play Store applications to receive updates by introducing two new actions to the App Manager:
- AllowApplicationUpgrade takes a package name and when specified, this package WILL be allowed to update from the Play Store.
- DisallowApplicationUpgrade also takes a package name and when specified, this package WILL NOT be allowed to update from the Play Store.
The existing Play Store update settings, e.g. "require AC power to perform updates", remain unaffected.
By default, the standard Android behaviour will apply, i.e., all applications will be automatically updated.
The features of MX are available through OEMConfig, EMDK and StageNow. To demonstrate how to disable Chrome from updating, I have used StageNow and configured the AppManager as follows:
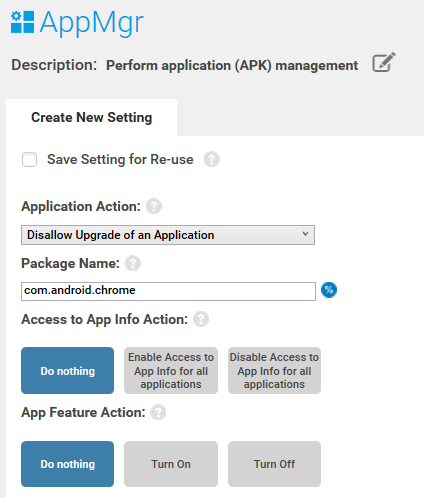
Note that MX10.3 requires StageNow 5.1 or higher to run. At the time of writing the AllowApplicationUpgrade / DisallowApplicationUpgrade has not yet made its way into OEMConfig.
My test device is a TC52 running Android 10. Build number: 10-16-10.00.QG-U44-STD-HEL-04 (The March 2021 LG release for BSP 10.16.10). This is the first LifeGuard patch that supports MX10.3 and is running version 10.3.0.18.
Out of the box, the device is running Chrome version 83.0.4103.96 but the latest version of Chrome in the Play Store is 89.0.4389.105.
By preventing Chrome from updating, you will see that the Play Store will download Chrome but the update will not be applied:
You can also see this video on YouTube at https://youtu.be/H5GCqnjljjk
Note that the WebView is also affected by disabling Chrome updates, this is a side effect of the WebView using the Chrome rendering engine.
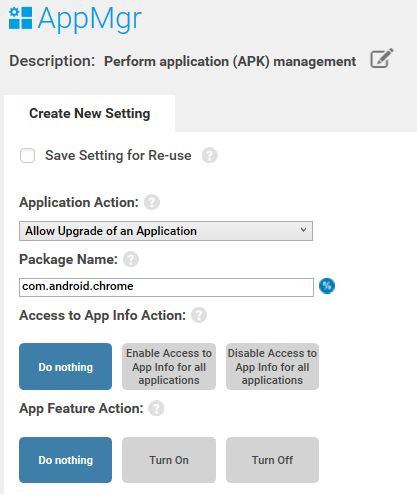
If you then “AllowApplicationUpgrade” again you will see that Chrome is now allowed to update from the Play Store.
Demonstrated using StageNow 5.1 as follows:
Updates will now be successfully applied:
This video is also available on YouTube: https://youtu.be/csOf8DYAoBY
In-app updates
The technique described above will also apply to In-app updates using the Play Core library, though this is rarely used in Enterprise.
Updates through the AppManager or Package Installer
The new “AllowApplicationUpgrade” / “DisallowApplicationUpgrade” actions were designed to be used with the Play Store but it is worth looking at how they impact application installation through some other means:
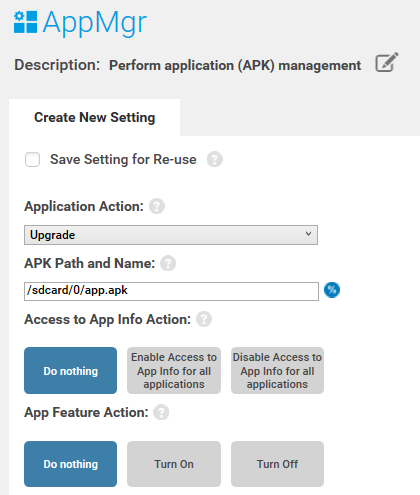
Applications updated via the AppManager
It is possible to update an application using the AppManager using the ‘Upgrade’ action. Again, you can do this with EMDK or StageNow but not OEMConfig (since the Device Owner would achieve the same result using the DPM API). In StageNow it will look like this:
Applications updated via the Package Installer
There are several ways the application update process can be kicked off using standard Android:
- An app can send an Intent with the ‘application/vnd.android.package-archive’ type.
- The user can select an .apk file using the file browser.
- The user can download an .apk file in Chrome and select it from Chrome downloads.
All of these techniques rely on the same underlying Android implementation to update the application, the Package Installer, though the installer itself cannot be invoked directly by non-system apps.
If you upgrade your application via the Package Installer then the upgrade will NOT SUCCEED if you have specified “DisallowApplicationUpgrade”
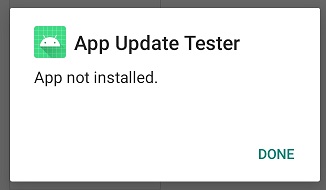
The above image shows an application which was copied to the device and selected from the file browser. Because the package was disallowed from upgrading, the upgrade did not succeed.
If you attempt to update the application via ADB you will receive the following message: "adb: failed to install
Conclusion:
Using the new features of AppManager it is now possible to have full control whether applications are upgraded from the Play Store or not. This provides the administrator with a much more granular control over their enterprise deployments.
Please note the following device requirements for this feature from https://techdocs.zebra.com/mx/appmgr/:
- SDM660 based devices: Android 10+, MX 10.3+, OSX10.5+
- Non-SDM660 based devices: Android Oreo+, MX10.3+, OSX8.13+ (or OSX10.5+ for devices running Android 10)
Please refer to your device's product reference guide to determine if the CPU is based on SDM660.

Darryn Campbell